2026 Data Breaches: Cybersecurity Incidents Explained
April 2026: Key Takeaways
April’s breach landscape was defined by one theme: attackers getting in through the side door. Every major incident this month traced back to a trusted third party — a vendor, a BPO contractor, or an OAuth-connected app. No front-door break-ins. No brute force. Just inherited access.
What happened in April:
- Two major U.S. banks (Citizens Financial and Frost Bank) were hit through a single shared vendor on the same day
- France’s national identity agency confirmed 11.7 million accounts compromised — with threat actors claiming up to 19 million
- Medtronic disclosed an unauthorized access incident with up to 9 million records claimed by ShinyHunters
- Adobe was reportedly breached through a third-party BPO support contractor via phishing and privilege escalation
- Vercel was compromised through a third-party AI tool with broad OAuth permissions — with a two-month dwell time before discovery
What security teams should take from this month:
- Your vendor’s security posture is now your security posture. Third-party risk isn’t a compliance checkbox — it’s your actual attack surface.
- The OAuth graph is the new perimeter. Most organizations have no inventory of which apps their employees have authorized.
- Persistent, data-centric encryption is the last line that holds. In every April incident, encrypted data would have been useless to the attacker after exfiltration.
Data Breaches from April 2026
April 2026 was dominated by supply-chain compromises and OAuth abuse. Two major U.S. banks were hit through a shared third-party vendor, a French government identity agency had records on millions of citizens offered for sale, a medical device giant faced a ShinyHunters extortion claim, Adobe was reportedly breached through an Indian BPO contractor, and an AI productivity tool became the entry point into a major cloud platform. Attackers are no longer breaking down the front door; they are walking in through trusted third parties. Knowing where sensitive data resides and protecting it accordingly remains the best assurance for breach resiliency.
Citizens Financial Group & Frost Bank
The Everest ransomware group posted both U.S. banks on its dark web leak site on April 20. The same-day leak involving shared document-production data points to a single-vendor compromise. Both banks confirmed the breach originated at an unnamed third-party vendor, not their own networks. Class action lawsuits were filed within days.
Scale of breach: 3.4 million records claimed from Citizens; over 250,000 SSNs and TINs from Frost.
Data exposed: Citizens — names, addresses, account numbers. Frost — names, addresses, Social Security numbers, taxpayer identification numbers, mortgage interest records, W-2s, 1099s, and HSA contributions.
Breach cause: Everest ransomware via a shared third-party vendor.
Source: Massachusetts Attorney General Data Breach Notification — https://www.mass.gov/lists/data-breach-notification-letters
Key Lessons
Two well-resourced banks blaming the same unnamed vendor on the same day means the vendor’s security posture became their security posture. The contrast between the datasets is instructive; Citizens’ exposure is largely to scams and profiling, while Frost’s is a near-complete identity-theft toolkit. Persistent encryption that travels with the data would have neutralized Frost’s exposure entirely; the hackers may have taken the files, but encrypted SSNs and tax records are useless without keys.
France Titres / ANTS (French Government)
France’s official issuer of national ID cards, passports, and driver’s licenses detected a breach on April 15. The next day, a threat actor known as “breach3d” listed the data for sale on a hacker forum. ANTS confirmed 11.7 million accounts were impacted and took the portal offline on April 24.
Scale of breach: 11.7 million accounts confirmed; threat actor claims up to 19 million records.
Data exposed: Login IDs, full names, email addresses, dates of birth, account identifiers, and, in some cases, postal addresses, place of birth, and phone numbers.
Breach cause: Undisclosed; investigation ongoing under CNIL, Paris Prosecutor, and ANSSI.
Source: ANTS Official Security Notice (ants.gouv.fr) — https://ants.gouv.fr/actualites/incident-de-securite
Key Lessons
Government identity database breaches are categorically more dangerous than commercial breaches because the data carries implicit authority. A scammer who knows a victim’s name, birthdate, and address sourced from the agency that issued their passport can run impersonations that random scraped data cannot match. Critical identity systems require data minimization, encryption that stays with the data, and continuous monitoring for anomalies in bulk exports.
Medtronic
Medical technology giant Medtronic confirmed on April 24, alongside an SEC Form 8-K filing, that an unauthorized party had accessed corporate IT systems. ShinyHunters claimed up to nine million records. Medtronic emphasized that hospital networks running their devices were not exposed.
Scale of breach: Up to 9 million records claimed by ShinyHunters; investigation ongoing.
Data exposed: Personal information and internal corporate data; specific types still being assessed.
Breach cause: ShinyHunters extortion attack; initial access vector not disclosed.
Source: SEC EDGAR — Medtronic Form 8-K Filing — https://www.sec.gov/cgi-bin/browse-edgar
Key Lessons
Medical device manufacturers carry both corporate and clinical risk surfaces, and the corporate-only framing only holds if segmentation is real. Medical records contain permanent identifiers; unlike credit cards, you cannot cancel your medical history. Persistent encryption on corporate-held customer and partner data limits what attackers can monetize, and automated discovery ensures regulated data does not drift into unprotected systems.
Adobe
A threat actor known as “Mr. Raccoon” allegedly breached Adobe through an Indian Business Process Outsourcing (BPO) firm contracted for support operations. The attacker delivered a Remote Access Tool via phishing, pivoted to a manager’s account, and reached the helpdesk environment, where a single agent could export all tickets in one request. Adobe has not publicly confirmed or denied the breach.
Scale of breach: 13 million customer support tickets, 15,000 employee records, and all HackerOne bug bounty submissions claimed.
Data exposed: Customer names, email addresses, account IDs, internal technical notes, and unpublished vulnerability reports.
Breach cause: Supply-chain compromise via third-party BPO; phishing followed by privilege escalation.
Source: International Cyber Security News — https://cybersecuritynews.com/adobe-breach/
Key Lessons
A single support agent being able to extract 13 million records in one query is an architectural gap, not a policy gap. The HackerOne submissions are the most damaging part; unpublished vulnerabilities could be weaponized before patches ship. Bulk export controls and DLP triggers on anomalous query volumes would have caught this. Persistent encryption on customer support data would have rendered the stolen tickets unusable after exfiltration.
Vercel (via Context.ai)
Vercel disclosed on April 19 that a Vercel employee’s Google Workspace account was compromised via Context.ai, a third-party AI tool granted broad OAuth permissions. The Context.ai compromise traced back to a Lumma Stealer infection in February, a two-month dwell time. The breach was discovered when the attacker listed the stolen data for $2 million on BreachForums.
Scale of breach: Limited customer subset; threat actor claims 580 employee records plus access keys, source code, and tokens.
Data exposed: Employee records, access keys, API keys, GitHub and NPM tokens, and non-sensitive environment variables.
Breach cause: OAuth supply-chain compromise via Lumma Stealer infection at Context.ai.
Source: Vercel Official Security Bulletin — https://vercel.com/kb/bulletin/vercel-april-2026-security-incident
Key Lessons
One employee granting broad Workspace permissions to a third-party AI tool gave attackers an inherited trust path into Vercel. The breach was not discovered by Vercel’s security team; it was discovered when the attacker chose to monetize publicly. The OAuth graph is now the new perimeter, and most companies have no inventory of which third-party apps their employees have authorized. Tightening OAuth scope reviews and inventorying authorized third-party apps would have closed the lateral path before it was used.
Data Breaches from March 2026
March was a volatile month for data breaches and ransomware. The most prominent was the attack on Stryker. While that incident didn’t expose data, it still had a significant effect on the company. As always, knowing where sensitive data is and remediating it accordingly provides you with the best assurance for breach resiliency.
Stryker
 Stryker, a medical device company, was recently the target of a hack deployed by an Iran-linked group, Handala. It caused system outages throughout the organization. It was not a ransomware attack. Rather, this was a data theft and wipe strike. Windows-based devices, including laptops and mobile devices, were wiped. As of March 30, the company had restored most manufacturing sites.
Stryker, a medical device company, was recently the target of a hack deployed by an Iran-linked group, Handala. It caused system outages throughout the organization. It was not a ransomware attack. Rather, this was a data theft and wipe strike. Windows-based devices, including laptops and mobile devices, were wiped. As of March 30, the company had restored most manufacturing sites.
- Scale of breach: Company applications and internal systems
- Breach cause: Handala gained access to the company’s Active Directory Services, using the Microsoft endpoint management tool, Microsoft Intune.
Key Lessons
This is a unique incident. Hackers didn’t steal data; they wiped in from internal systems, which triggered operational fallout. The attack on endpoint systems wasn’t to exfiltrate or hold for ransom; it was about disruption.
When there’s a compromise to endpoints, cyber criminals can deploy software to wipe, encrypt, or exfiltrate data as well as disable security mechanisms.
While you cannot eliminate this risk, you can do these things:
Ensure automated sensitive data discovery, so you always know where data is.
Use policy-based protection to determine what to do with the discovered data consistently (e.g., encrypt, mask, redact, etc.).
Enable persistent encryption that stays with data regardless of where it goes.
Aura
Aura announced a data breach via a targeted phishing attack that led to the exposure of marketing data lists. The company identified the breach within an hour and activated its incident response plan. Aura announced that the hack did not expose any sensitive data.
- Scale of breach: 900,000 records
- Data exposed: Names and email addresses
- Breach cause: ShinyHunters claimed responsibility via a phishing attack.
- Data breach notifications: See Aura’s statement here.
Key Lessons
Aura did an excellent job of responding quickly. Often, it takes weeks or even months to detect unauthorized access. Even though data stolen wasn’t sensitive, it’s still a reminder that organizations should deploy data-centric encryption, which is “sticky.” It stays with the data no matter where it goes.
Data breach resiliency strategies can reduce the effects of ransomware. Such programs involve enterprise-wide visibility of sensitive data and preemptive protections, such as encryption, masking, and redaction.
Navia
 An exposed API was a weak link for an attacker to gain unauthorized access. The hackers stole personal and health-related data. Their investigation revealed that the threat actor acquired information from December 22, 2025, to January 15, 2026.
An exposed API was a weak link for an attacker to gain unauthorized access. The hackers stole personal and health-related data. Their investigation revealed that the threat actor acquired information from December 22, 2025, to January 15, 2026.
- Scale of breach: 2.7 million people
- Data exposed: Social Security numbers, account data, names, dates of birth, phone numbers, email addresses, and health plan information
- Breach cause: Exposed API
- Data breach notifications: Read Navia’s notice here.
Key Lessons
Perimeter defenses were insufficient to thwart unauthorized actors. They stole PII and PHI; data that should be encrypted at rest and in transit. Persistent encryption driven by enterprise-wide policies could have made a difference. The hackers may have taken the data, but with encryption, it would have been unusable.
Pathstone Family Office
Pathstone Family Office, a wealth management firm, was the victim of a data breach perpetrated by ShinyHunters. The theft included 641,000 records of sensitive and proprietary information. The group attempted to extort Pathstone Family Office, threatening to release data.
- Scale of breach: 641,000 records
- Data exposed: Social Security numbers, dates of birth, addresses, and potentially detailed financial profiles of clients
- Breach cause: ShinyHunters ransomware
Key Lessons
Attorneys filed a class action against Pathstone, alleging inadequate cybersecurity practices and noncompliance. Those claims will have to play out in court. Pathstone has yet to issue breach notifications or public responses. Any breach indicates a gap in perimeter security; access controls likely failed. Modern encryption that stays with data could have rendered it useless to the cyber criminals.
University of Hawaiʻi
The University of Hawaiʻi was the victim of a ransomware attack. It impacted research systems, exposing personal information.
- Scale of breach: 1.2 million individuals
- Data exposed: Social Security numbers, driver’s license details, and health-related research information
- Breach cause: Ransomware
- Breach notification: See the statement from the university here.
Key Lessons
An unauthorized user was able to encrypt and exfiltrate data during the attack. UH said that they have no reports of hackers publishing any stolen data. They continue to investigate the root cause. This incident brings to the forefront the discussion on knowing where all sensitive data resides.
The breached files were part of a subset and were collected between 1993 and 2007. This was likely old data that UH may no longer have needed to keep. It could have been “forgotten data,” which carries risk. Having policies in place to delete or remove old data would have potentially prevented this.
Data Breaches from February 2026
Even though February is a short month, there were numerous 2026 data breaches. Healthcare, fintech, marketplaces, and publishing platforms all experienced incidents. Many involve lawsuits from customers.
BridgePay
BridgePay, a payments platform, confirmed a ransomware attack that led to a system disruption. City governments are a large part of the company’s customer base, and many reported outages. As of February 28, BridgePay had restored all its infrastructure.
- Scale of breach: The company stated there was no exposure of credit card numbers.
- Data exposed: Unknown
- Breach cause: Ransomware
- Data breach notifications: BridgePay’s statement
Key Lessons
Ransomware continues to be a risk for any organization. Proactively securing data against it is your best approach. Key components of a proactive data security program include automated data discovery and protection. Discovery is a critical first step since you must know where all sensitive information is to protect it.
Using policy-driven protection controls enables you to define them centrally and apply them consistently across your enterprise. You can also ensure secure data exchange with certificate-free, modern encryption.
University of Mississippi Medical Center
 The University of Mississippi Medical Center closed clinics after a ransomware attack in February. The impact included IT systems and EHRs, requiring manual processes for patient care. They were able to reopen clinics on March 2.
The University of Mississippi Medical Center closed clinics after a ransomware attack in February. The impact included IT systems and EHRs, requiring manual processes for patient care. They were able to reopen clinics on March 2.
- Scale of breach: Impacted data included phone and email access. It also forced clinicians to move to downtime procedures.
- Data exposed: The organization has not disclosed whether there was any breach of PII or PHI.
- Breach cause: Ransomware
- Data breach notifications: The organization has yet to send any data breach notifications. They announced the issue on their social media profiles and published a statement on March 2 about reopening clinics.
Key Lessons
Healthcare remains an attractive target for ransomware. Few are ready, as almost 40% of organizations facing an incident took a month or more to recover.
Data breach resiliency strategies can reduce the effects of ransomware. Such programs involve enterprise-wide visibility of sensitive data and preemptive protections, such as encryption, masking, and redaction.
Marquis Health
Over 780,000 people had their information stolen in this healthcare data breach. The company detected the breach in 2025. It only recently came to light when the organized issued breach notifications in multiple states. Marquis stated that the SonicWall hack was to blame and has since filed suit against them.
- Scale of breach: 780,000 individuals
- Data exposed: Names, addresses, Social Security numbers, dates of birth, account numbers, credit/debit card numbers, and taxpayer identification numbers
- Breach cause: Ransomware breach on SonicWall cloud backup hack
- Data breach notifications:
Key Lessons
The source of the breach was Marquis’s cybersecurity partner, SonicWall, as alleged in their lawsuit. Marquis’s investigation found that the attacker leveraged configuration data extracted from SonicWall’s cloud backup infrastructure tied to an API code change.
Marquis also stated its firewall was up to date and had other security controls in place, including MFA.
This incident underscores the importance of auditing partners that support technology, networks, or other infrastructure. Additionally, companies must take steps to ensure exfiltrated data isn’t usable by encrypting, masking, or redacting it properly and consistently.
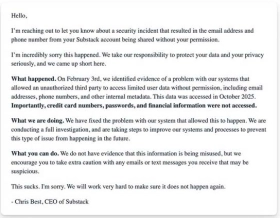
Substack
Substack, a subscription-based publishing platform, suffered a data breach that exposed subscriber information. The company confirmed that no passwords, payment card data, or financial records were part of the incident.
- Scale of breach: Unknown
- Data exposed: Email addresses and phone numbers
- Breach cause: Unauthorized third-party access
- Data breach notifications: The company sent this email to users.
Key Lessons
Since the hacker had limited account access, there was no PII or PHI breached. However, this incident serves as a warning against depending too much on perimeter controls as the last line of defense. Unfortunately, weaknesses are common here. The best way to bolster defenses is with data-centric protections that are always present. When data has persistent protection, if stolen, data is typically unusable.
CarGurus
CarGurus, an online automotive marketplace, revealed a data breach affecting over 12 million users. An Australian cybersecurity consultant, Troy Hunt, was the first to report this after finding published PII data.
The company reported a system compromise involving stored customer account information. They investigated, secured the impacted platforms, and implemented more safeguards in response. Victims have filed class action lawsuits.
- Scale of breach: 12 million+
- Data exposed: Names, email addresses, physical addresses, IP addresses, and phone numbers
- Breach cause: ShinyHunters claimed responsibility via social engineering.
- Data breach notifications: One lawsuit alleges that CarGurus did not provide a data breach notice. There are no formal notices, but the company did acknowledge it, stating it was “limited in scope.”
Key Lessons
Employees can be a weak link in cybersecurity. While training helps, hackers have become very sophisticated in their social engineering attacks. As such, you can’t always count on employees to recognize and report phishing.
To further safeguard data against such a breach, persistent, modern encryption should be part of a data protection program. When it is, it never leaves the data, so anything hackers steal won’t be of value if they can’t decrypt it.
Data Breaches from January 2026
We’re kicking off 2026 data breaches with a review of January. The incidents in January cover multiple industries. What’s unique about this batch is that there was exposure of both consumer and corporate data. Explore the cases in January and the key insights into preventing these in your organization.
Illinois and Minnesota Department of Human Services
Both Illinois and Minnesota experienced a system failure that exposed the personal data of nearly one million people. In the Illinois incident, sensitive information was on display publicly and was visible for four years.
The Minnesota breach was the result of excessive internal access, leading to improper disclosure.
- Scale of breach: Around one million individuals
- Data exposed: Names, addresses, case numbers, case status, and referral information (Illinois); names, addresses, email addresses, dates of birth, phone numbers, Medicaid ID, the first four digits of Social Security numbers, and other protected information (Minnesota).
- Breach cause: In Illinois, an error caused patient data to be publicly viewable. In Minnesota, the culprit was unauthorized access to data that was outside the scope of employee work assignments.
- Data breach notifications:
- Report from HIPAA Journal (Illinois)
- DHS Notification (Minnesota)
Key Lessons
It's imperative for every organization to have complete visibility of where sensitive data resides. Automated discovery provides this visibility enterprise-wide and centralized, policy-based protection ensures consistent security of data. For four years, the data of Illinois residents was available online. Having an always-up-to-date inventory with data-centric protection can prevent such exposure.
Identity access control (IAC) plays a key role in thwarting unauthorized access, but relying on it as the last line of defense has shortcomings. IAC doesn't truly protect your critical data and sensitive data can be exposed if data moves or credentials are compromised. Protecting data through encryption, masking, or redaction secures data at rest and in motion and ensures that exfiltrated data is useless to bad actors.
Ledger and Global-e
Ledger, a crypto wallet platform, confirmed a customer data breach related to its e-commerce payment partner, Global-e. While there were no crypto assets stolen, hackers later used this information in phishing campaigns.
- Scale of breach: Unknown
- Data exposed: Name, addresses, email addresses, phone numbers, and order details.
- Breach cause: The company identified unusual activity in its cloud systems and moved to secure it. They did not disclose the root cause.
- Data breach notification: Global-e Statement
Key Lessons
Companies should adopt persistent encryption and protection across all environments. With such a proactive strategy in place, organizations can protect across the enterprise. When security is data-centric, it reduces the effect of breaches.
Cloud-Sharing Sites
 The threat actor Zestix has been selling corporate data stolen from multiple companies. They are acting as an initial access broker (IAB) on the dark web. The hack occurred due to stolen credentials. ShareFile, Nextcloud, and OwnCloud were all victims of the attack. There were impacted organizations across many sectors, including aviation, defense, healthcare, utilities, mass transit, telecom, legal, real estate, and government.
The threat actor Zestix has been selling corporate data stolen from multiple companies. They are acting as an initial access broker (IAB) on the dark web. The hack occurred due to stolen credentials. ShareFile, Nextcloud, and OwnCloud were all victims of the attack. There were impacted organizations across many sectors, including aviation, defense, healthcare, utilities, mass transit, telecom, legal, real estate, and government.
- Scale of breach: Unknown
- Data exposed: Highly sensitive corporate data, including health records and government contracts.
- Breach cause: Stolen credentials and lack of multi-factor authentication
- Breach investigation: Infostealers published a detailed analysis of the hacks.
Key Lessons
Cloud exposure has been a risk component for many years. MFA has become mandatory in many regulations. Will this alone be enough to reduce unauthorized access? No, but enterprise-wide data encryption, redaction, and masking limit the fallout of such an attack.
Nike
On January 24, Nike launched an investigation into a possible cyber attack. This action came after WorldLeaks claimed it had stolen and posted 1.4 terabytes of internal company data.
- Scale of breach: 1.4 terabytes of company data
- Date exposed: Product development intellectual property and supply chain logistics
- Breach cause: Not defined, but threat intelligence firms have suggested a connection to supply chain infrastructure.
- Breach report: The National CIO Review provided an extensive review of the attack and leak.
Key Lessons
This data breach involves corporate data versus customer data. Investigators did not find personal identifiers. However, the leak of IP and other trade secrets could have been of value to competitors.
Organizations should enforce security controls and cybersecurity best practices with supply chain vendors. Additionally, security embedded into data follows it wherever it goes.
Crunchbase
Crunchbase confirmed a data breach in January after a hack. ShinyHunters, a cybercrime group, claimed responsibility. The company revealed there was file exfiltration but said there were no operational disruptions. The incident is still under investigation, and they have yet to send any notifications to customers.
- Scale of breach: Two million records
- Data exposed: PII and corporate data (e.g., contracts and internal documents)
- Breach cause: Social engineering campaign using voice phishing techniques
- Breach report: SecurityWeek was the first to report the story and received confirmation from Crunchbase.
Key Lessons
Social engineering, especially deepfakes, is much more sophisticated than ever before. They are emerging as a key way for hackers to compromise credentials. While you can't eliminate all breach risk, you can take proactive steps to minimize the impact. Examples include:
- Identifying older files and enforcing data retention policies
- Using encryption mechanisms that stay with data
- Applying data discovery and classification solutions to build an inventory of sensitive information
Match Group
 The family of Match dating apps finishes out the list of the major 2026 data breaches in January. ShinyHunters was also the cyber criminal in this case. The group claimed they have millions of documents, while Match called it a "security incident" that is still under investigation.
The family of Match dating apps finishes out the list of the major 2026 data breaches in January. ShinyHunters was also the cyber criminal in this case. The group claimed they have millions of documents, while Match called it a "security incident" that is still under investigation.
- Scale of breach: 10 million records
- Data exposed: User and corporate data
- Breach cause: According to ShinyHunters dark web leak site, it cited AppsFlyer as the entry point. AppsFlyer is a marketing analytics company for apps.
- Breach report: The Register published a review of the breach and exposures.
Key Lessons
It appears this is another third-party system failure. Data sharing for analytics is essential to any business but carries risk. Secure data exchange, internally or externally, with modern encryption allows for access while safeguarding data.
April 2026: Key Takeaways
April’s breach landscape was defined by one theme: attackers getting in through the side door. Every major incident this month traced back to a trusted third party — a vendor, a BPO contractor, or an OAuth-connected app. No front-door break-ins. No brute force. Just inherited access.
What happened in April:
- Two major U.S. banks (Citizens Financial and Frost Bank) were hit through a single shared vendor on the same day
- France’s national identity agency confirmed 11.7 million accounts compromised — with threat actors claiming up to 19 million
- Medtronic disclosed an unauthorized access incident with up to 9 million records claimed by ShinyHunters
- Adobe was reportedly breached through a third-party BPO support contractor via phishing and privilege escalation
- Vercel was compromised through a third-party AI tool with broad OAuth permissions — with a two-month dwell time before discovery
What security teams should take from this month:
- Your vendor’s security posture is now your security posture. Third-party risk isn’t a compliance checkbox — it’s your actual attack surface.
- The OAuth graph is the new perimeter. Most organizations have no inventory of which apps their employees have authorized.
- Persistent, data-centric encryption is the last line that holds. In every April incident, encrypted data would have been useless to the attacker after exfiltration.
Data Breaches from April 2026
April 2026 was dominated by supply-chain compromises and OAuth abuse. Two major U.S. banks were hit through a shared third-party vendor, a French government identity agency had records on millions of citizens offered for sale, a medical device giant faced a ShinyHunters extortion claim, Adobe was reportedly breached through an Indian BPO contractor, and an AI productivity tool became the entry point into a major cloud platform. Attackers are no longer breaking down the front door; they are walking in through trusted third parties. Knowing where sensitive data resides and protecting it accordingly remains the best assurance for breach resiliency.
Citizens Financial Group & Frost Bank
The Everest ransomware group posted both U.S. banks on its dark web leak site on April 20. The same-day leak involving shared document-production data points to a single-vendor compromise. Both banks confirmed the breach originated at an unnamed third-party vendor, not their own networks. Class action lawsuits were filed within days.
Scale of breach: 3.4 million records claimed from Citizens; over 250,000 SSNs and TINs from Frost.
Data exposed: Citizens — names, addresses, account numbers. Frost — names, addresses, Social Security numbers, taxpayer identification numbers, mortgage interest records, W-2s, 1099s, and HSA contributions.
Breach cause: Everest ransomware via a shared third-party vendor.
Source: Massachusetts Attorney General Data Breach Notification — https://www.mass.gov/lists/data-breach-notification-letters
Key Lessons
Two well-resourced banks blaming the same unnamed vendor on the same day means the vendor’s security posture became their security posture. The contrast between the datasets is instructive; Citizens’ exposure is largely to scams and profiling, while Frost’s is a near-complete identity-theft toolkit. Persistent encryption that travels with the data would have neutralized Frost’s exposure entirely; the hackers may have taken the files, but encrypted SSNs and tax records are useless without keys.
France Titres / ANTS (French Government)
France’s official issuer of national ID cards, passports, and driver’s licenses detected a breach on April 15. The next day, a threat actor known as “breach3d” listed the data for sale on a hacker forum. ANTS confirmed 11.7 million accounts were impacted and took the portal offline on April 24.
Scale of breach: 11.7 million accounts confirmed; threat actor claims up to 19 million records.
Data exposed: Login IDs, full names, email addresses, dates of birth, account identifiers, and, in some cases, postal addresses, place of birth, and phone numbers.
Breach cause: Undisclosed; investigation ongoing under CNIL, Paris Prosecutor, and ANSSI.
Source: ANTS Official Security Notice (ants.gouv.fr) — https://ants.gouv.fr/actualites/incident-de-securite
Key Lessons
Government identity database breaches are categorically more dangerous than commercial breaches because the data carries implicit authority. A scammer who knows a victim’s name, birthdate, and address sourced from the agency that issued their passport can run impersonations that random scraped data cannot match. Critical identity systems require data minimization, encryption that stays with the data, and continuous monitoring for anomalies in bulk exports.
Medtronic
Medical technology giant Medtronic confirmed on April 24, alongside an SEC Form 8-K filing, that an unauthorized party had accessed corporate IT systems. ShinyHunters claimed up to nine million records. Medtronic emphasized that hospital networks running their devices were not exposed.
Scale of breach: Up to 9 million records claimed by ShinyHunters; investigation ongoing.
Data exposed: Personal information and internal corporate data; specific types still being assessed.
Breach cause: ShinyHunters extortion attack; initial access vector not disclosed.
Source: SEC EDGAR — Medtronic Form 8-K Filing — https://www.sec.gov/cgi-bin/browse-edgar
Key Lessons
Medical device manufacturers carry both corporate and clinical risk surfaces, and the corporate-only framing only holds if segmentation is real. Medical records contain permanent identifiers; unlike credit cards, you cannot cancel your medical history. Persistent encryption on corporate-held customer and partner data limits what attackers can monetize, and automated discovery ensures regulated data does not drift into unprotected systems.
Adobe
A threat actor known as “Mr. Raccoon” allegedly breached Adobe through an Indian Business Process Outsourcing (BPO) firm contracted for support operations. The attacker delivered a Remote Access Tool via phishing, pivoted to a manager’s account, and reached the helpdesk environment, where a single agent could export all tickets in one request. Adobe has not publicly confirmed or denied the breach.
Scale of breach: 13 million customer support tickets, 15,000 employee records, and all HackerOne bug bounty submissions claimed.
Data exposed: Customer names, email addresses, account IDs, internal technical notes, and unpublished vulnerability reports.
Breach cause: Supply-chain compromise via third-party BPO; phishing followed by privilege escalation.
Source: International Cyber Security News — https://cybersecuritynews.com/adobe-breach/
Key Lessons
A single support agent being able to extract 13 million records in one query is an architectural gap, not a policy gap. The HackerOne submissions are the most damaging part; unpublished vulnerabilities could be weaponized before patches ship. Bulk export controls and DLP triggers on anomalous query volumes would have caught this. Persistent encryption on customer support data would have rendered the stolen tickets unusable after exfiltration.
Vercel (via Context.ai)
Vercel disclosed on April 19 that a Vercel employee’s Google Workspace account was compromised via Context.ai, a third-party AI tool granted broad OAuth permissions. The Context.ai compromise traced back to a Lumma Stealer infection in February, a two-month dwell time. The breach was discovered when the attacker listed the stolen data for $2 million on BreachForums.
Scale of breach: Limited customer subset; threat actor claims 580 employee records plus access keys, source code, and tokens.
Data exposed: Employee records, access keys, API keys, GitHub and NPM tokens, and non-sensitive environment variables.
Breach cause: OAuth supply-chain compromise via Lumma Stealer infection at Context.ai.
Source: Vercel Official Security Bulletin — https://vercel.com/kb/bulletin/vercel-april-2026-security-incident
Key Lessons
One employee granting broad Workspace permissions to a third-party AI tool gave attackers an inherited trust path into Vercel. The breach was not discovered by Vercel’s security team; it was discovered when the attacker chose to monetize publicly. The OAuth graph is now the new perimeter, and most companies have no inventory of which third-party apps their employees have authorized. Tightening OAuth scope reviews and inventorying authorized third-party apps would have closed the lateral path before it was used.
Data Breaches from March 2026
March was a volatile month for data breaches and ransomware. The most prominent was the attack on Stryker. While that incident didn’t expose data, it still had a significant effect on the company. As always, knowing where sensitive data is and remediating it accordingly provides you with the best assurance for breach resiliency.
Stryker
 Stryker, a medical device company, was recently the target of a hack deployed by an Iran-linked group, Handala. It caused system outages throughout the organization. It was not a ransomware attack. Rather, this was a data theft and wipe strike. Windows-based devices, including laptops and mobile devices, were wiped. As of March 30, the company had restored most manufacturing sites.
Stryker, a medical device company, was recently the target of a hack deployed by an Iran-linked group, Handala. It caused system outages throughout the organization. It was not a ransomware attack. Rather, this was a data theft and wipe strike. Windows-based devices, including laptops and mobile devices, were wiped. As of March 30, the company had restored most manufacturing sites.
- Scale of breach: Company applications and internal systems
- Breach cause: Handala gained access to the company’s Active Directory Services, using the Microsoft endpoint management tool, Microsoft Intune.
Key Lessons
This is a unique incident. Hackers didn’t steal data; they wiped in from internal systems, which triggered operational fallout. The attack on endpoint systems wasn’t to exfiltrate or hold for ransom; it was about disruption.
When there’s a compromise to endpoints, cyber criminals can deploy software to wipe, encrypt, or exfiltrate data as well as disable security mechanisms.
While you cannot eliminate this risk, you can do these things:
Ensure automated sensitive data discovery, so you always know where data is.
Use policy-based protection to determine what to do with the discovered data consistently (e.g., encrypt, mask, redact, etc.).
Enable persistent encryption that stays with data regardless of where it goes.
Aura
Aura announced a data breach via a targeted phishing attack that led to the exposure of marketing data lists. The company identified the breach within an hour and activated its incident response plan. Aura announced that the hack did not expose any sensitive data.
- Scale of breach: 900,000 records
- Data exposed: Names and email addresses
- Breach cause: ShinyHunters claimed responsibility via a phishing attack.
- Data breach notifications: See Aura’s statement here.
Key Lessons
Aura did an excellent job of responding quickly. Often, it takes weeks or even months to detect unauthorized access. Even though data stolen wasn’t sensitive, it’s still a reminder that organizations should deploy data-centric encryption, which is “sticky.” It stays with the data no matter where it goes.
Data breach resiliency strategies can reduce the effects of ransomware. Such programs involve enterprise-wide visibility of sensitive data and preemptive protections, such as encryption, masking, and redaction.
Navia
 An exposed API was a weak link for an attacker to gain unauthorized access. The hackers stole personal and health-related data. Their investigation revealed that the threat actor acquired information from December 22, 2025, to January 15, 2026.
An exposed API was a weak link for an attacker to gain unauthorized access. The hackers stole personal and health-related data. Their investigation revealed that the threat actor acquired information from December 22, 2025, to January 15, 2026.
- Scale of breach: 2.7 million people
- Data exposed: Social Security numbers, account data, names, dates of birth, phone numbers, email addresses, and health plan information
- Breach cause: Exposed API
- Data breach notifications: Read Navia’s notice here.
Key Lessons
Perimeter defenses were insufficient to thwart unauthorized actors. They stole PII and PHI; data that should be encrypted at rest and in transit. Persistent encryption driven by enterprise-wide policies could have made a difference. The hackers may have taken the data, but with encryption, it would have been unusable.
Pathstone Family Office
Pathstone Family Office, a wealth management firm, was the victim of a data breach perpetrated by ShinyHunters. The theft included 641,000 records of sensitive and proprietary information. The group attempted to extort Pathstone Family Office, threatening to release data.
- Scale of breach: 641,000 records
- Data exposed: Social Security numbers, dates of birth, addresses, and potentially detailed financial profiles of clients
- Breach cause: ShinyHunters ransomware
Key Lessons
Attorneys filed a class action against Pathstone, alleging inadequate cybersecurity practices and noncompliance. Those claims will have to play out in court. Pathstone has yet to issue breach notifications or public responses. Any breach indicates a gap in perimeter security; access controls likely failed. Modern encryption that stays with data could have rendered it useless to the cyber criminals.
University of Hawaiʻi
The University of Hawaiʻi was the victim of a ransomware attack. It impacted research systems, exposing personal information.
- Scale of breach: 1.2 million individuals
- Data exposed: Social Security numbers, driver’s license details, and health-related research information
- Breach cause: Ransomware
- Breach notification: See the statement from the university here.
Key Lessons
An unauthorized user was able to encrypt and exfiltrate data during the attack. UH said that they have no reports of hackers publishing any stolen data. They continue to investigate the root cause. This incident brings to the forefront the discussion on knowing where all sensitive data resides.
The breached files were part of a subset and were collected between 1993 and 2007. This was likely old data that UH may no longer have needed to keep. It could have been “forgotten data,” which carries risk. Having policies in place to delete or remove old data would have potentially prevented this.
Data Breaches from February 2026
Even though February is a short month, there were numerous 2026 data breaches. Healthcare, fintech, marketplaces, and publishing platforms all experienced incidents. Many involve lawsuits from customers.
BridgePay
BridgePay, a payments platform, confirmed a ransomware attack that led to a system disruption. City governments are a large part of the company’s customer base, and many reported outages. As of February 28, BridgePay had restored all its infrastructure.
- Scale of breach: The company stated there was no exposure of credit card numbers.
- Data exposed: Unknown
- Breach cause: Ransomware
- Data breach notifications: BridgePay’s statement
Key Lessons
Ransomware continues to be a risk for any organization. Proactively securing data against it is your best approach. Key components of a proactive data security program include automated data discovery and protection. Discovery is a critical first step since you must know where all sensitive information is to protect it.
Using policy-driven protection controls enables you to define them centrally and apply them consistently across your enterprise. You can also ensure secure data exchange with certificate-free, modern encryption.
University of Mississippi Medical Center
 The University of Mississippi Medical Center closed clinics after a ransomware attack in February. The impact included IT systems and EHRs, requiring manual processes for patient care. They were able to reopen clinics on March 2.
The University of Mississippi Medical Center closed clinics after a ransomware attack in February. The impact included IT systems and EHRs, requiring manual processes for patient care. They were able to reopen clinics on March 2.
- Scale of breach: Impacted data included phone and email access. It also forced clinicians to move to downtime procedures.
- Data exposed: The organization has not disclosed whether there was any breach of PII or PHI.
- Breach cause: Ransomware
- Data breach notifications: The organization has yet to send any data breach notifications. They announced the issue on their social media profiles and published a statement on March 2 about reopening clinics.
Key Lessons
Healthcare remains an attractive target for ransomware. Few are ready, as almost 40% of organizations facing an incident took a month or more to recover.
Data breach resiliency strategies can reduce the effects of ransomware. Such programs involve enterprise-wide visibility of sensitive data and preemptive protections, such as encryption, masking, and redaction.
Marquis Health
Over 780,000 people had their information stolen in this healthcare data breach. The company detected the breach in 2025. It only recently came to light when the organized issued breach notifications in multiple states. Marquis stated that the SonicWall hack was to blame and has since filed suit against them.
- Scale of breach: 780,000 individuals
- Data exposed: Names, addresses, Social Security numbers, dates of birth, account numbers, credit/debit card numbers, and taxpayer identification numbers
- Breach cause: Ransomware breach on SonicWall cloud backup hack
- Data breach notifications:
Key Lessons
The source of the breach was Marquis’s cybersecurity partner, SonicWall, as alleged in their lawsuit. Marquis’s investigation found that the attacker leveraged configuration data extracted from SonicWall’s cloud backup infrastructure tied to an API code change.
Marquis also stated its firewall was up to date and had other security controls in place, including MFA.
This incident underscores the importance of auditing partners that support technology, networks, or other infrastructure. Additionally, companies must take steps to ensure exfiltrated data isn’t usable by encrypting, masking, or redacting it properly and consistently.
Substack
Substack, a subscription-based publishing platform, suffered a data breach that exposed subscriber information. The company confirmed that no passwords, payment card data, or financial records were part of the incident.
- Scale of breach: Unknown
- Data exposed: Email addresses and phone numbers
- Breach cause: Unauthorized third-party access
- Data breach notifications: The company sent this email to users.
Key Lessons
Since the hacker had limited account access, there was no PII or PHI breached. However, this incident serves as a warning against depending too much on perimeter controls as the last line of defense. Unfortunately, weaknesses are common here. The best way to bolster defenses is with data-centric protections that are always present. When data has persistent protection, if stolen, data is typically unusable.
CarGurus
CarGurus, an online automotive marketplace, revealed a data breach affecting over 12 million users. An Australian cybersecurity consultant, Troy Hunt, was the first to report this after finding published PII data.
The company reported a system compromise involving stored customer account information. They investigated, secured the impacted platforms, and implemented more safeguards in response. Victims have filed class action lawsuits.
- Scale of breach: 12 million+
- Data exposed: Names, email addresses, physical addresses, IP addresses, and phone numbers
- Breach cause: ShinyHunters claimed responsibility via social engineering.
- Data breach notifications: One lawsuit alleges that CarGurus did not provide a data breach notice. There are no formal notices, but the company did acknowledge it, stating it was “limited in scope.”
Key Lessons
Employees can be a weak link in cybersecurity. While training helps, hackers have become very sophisticated in their social engineering attacks. As such, you can’t always count on employees to recognize and report phishing.
To further safeguard data against such a breach, persistent, modern encryption should be part of a data protection program. When it is, it never leaves the data, so anything hackers steal won’t be of value if they can’t decrypt it.
Data Breaches from January 2026
We’re kicking off 2026 data breaches with a review of January. The incidents in January cover multiple industries. What’s unique about this batch is that there was exposure of both consumer and corporate data. Explore the cases in January and the key insights into preventing these in your organization.
Illinois and Minnesota Department of Human Services
Both Illinois and Minnesota experienced a system failure that exposed the personal data of nearly one million people. In the Illinois incident, sensitive information was on display publicly and was visible for four years.
The Minnesota breach was the result of excessive internal access, leading to improper disclosure.
- Scale of breach: Around one million individuals
- Data exposed: Names, addresses, case numbers, case status, and referral information (Illinois); names, addresses, email addresses, dates of birth, phone numbers, Medicaid ID, the first four digits of Social Security numbers, and other protected information (Minnesota).
- Breach cause: In Illinois, an error caused patient data to be publicly viewable. In Minnesota, the culprit was unauthorized access to data that was outside the scope of employee work assignments.
- Data breach notifications:
- Report from HIPAA Journal (Illinois)
- DHS Notification (Minnesota)
Key Lessons
It's imperative for every organization to have complete visibility of where sensitive data resides. Automated discovery provides this visibility enterprise-wide and centralized, policy-based protection ensures consistent security of data. For four years, the data of Illinois residents was available online. Having an always-up-to-date inventory with data-centric protection can prevent such exposure.
Identity access control (IAC) plays a key role in thwarting unauthorized access, but relying on it as the last line of defense has shortcomings. IAC doesn't truly protect your critical data and sensitive data can be exposed if data moves or credentials are compromised. Protecting data through encryption, masking, or redaction secures data at rest and in motion and ensures that exfiltrated data is useless to bad actors.
Ledger and Global-e
Ledger, a crypto wallet platform, confirmed a customer data breach related to its e-commerce payment partner, Global-e. While there were no crypto assets stolen, hackers later used this information in phishing campaigns.
- Scale of breach: Unknown
- Data exposed: Name, addresses, email addresses, phone numbers, and order details.
- Breach cause: The company identified unusual activity in its cloud systems and moved to secure it. They did not disclose the root cause.
- Data breach notification: Global-e Statement
Key Lessons
Companies should adopt persistent encryption and protection across all environments. With such a proactive strategy in place, organizations can protect across the enterprise. When security is data-centric, it reduces the effect of breaches.
Cloud-Sharing Sites
 The threat actor Zestix has been selling corporate data stolen from multiple companies. They are acting as an initial access broker (IAB) on the dark web. The hack occurred due to stolen credentials. ShareFile, Nextcloud, and OwnCloud were all victims of the attack. There were impacted organizations across many sectors, including aviation, defense, healthcare, utilities, mass transit, telecom, legal, real estate, and government.
The threat actor Zestix has been selling corporate data stolen from multiple companies. They are acting as an initial access broker (IAB) on the dark web. The hack occurred due to stolen credentials. ShareFile, Nextcloud, and OwnCloud were all victims of the attack. There were impacted organizations across many sectors, including aviation, defense, healthcare, utilities, mass transit, telecom, legal, real estate, and government.
- Scale of breach: Unknown
- Data exposed: Highly sensitive corporate data, including health records and government contracts.
- Breach cause: Stolen credentials and lack of multi-factor authentication
- Breach investigation: Infostealers published a detailed analysis of the hacks.
Key Lessons
Cloud exposure has been a risk component for many years. MFA has become mandatory in many regulations. Will this alone be enough to reduce unauthorized access? No, but enterprise-wide data encryption, redaction, and masking limit the fallout of such an attack.
Nike
On January 24, Nike launched an investigation into a possible cyber attack. This action came after WorldLeaks claimed it had stolen and posted 1.4 terabytes of internal company data.
- Scale of breach: 1.4 terabytes of company data
- Date exposed: Product development intellectual property and supply chain logistics
- Breach cause: Not defined, but threat intelligence firms have suggested a connection to supply chain infrastructure.
- Breach report: The National CIO Review provided an extensive review of the attack and leak.
Key Lessons
This data breach involves corporate data versus customer data. Investigators did not find personal identifiers. However, the leak of IP and other trade secrets could have been of value to competitors.
Organizations should enforce security controls and cybersecurity best practices with supply chain vendors. Additionally, security embedded into data follows it wherever it goes.
Crunchbase
Crunchbase confirmed a data breach in January after a hack. ShinyHunters, a cybercrime group, claimed responsibility. The company revealed there was file exfiltration but said there were no operational disruptions. The incident is still under investigation, and they have yet to send any notifications to customers.
- Scale of breach: Two million records
- Data exposed: PII and corporate data (e.g., contracts and internal documents)
- Breach cause: Social engineering campaign using voice phishing techniques
- Breach report: SecurityWeek was the first to report the story and received confirmation from Crunchbase.
Key Lessons
Social engineering, especially deepfakes, is much more sophisticated than ever before. They are emerging as a key way for hackers to compromise credentials. While you can't eliminate all breach risk, you can take proactive steps to minimize the impact. Examples include:
- Identifying older files and enforcing data retention policies
- Using encryption mechanisms that stay with data
- Applying data discovery and classification solutions to build an inventory of sensitive information
Match Group
 The family of Match dating apps finishes out the list of the major 2026 data breaches in January. ShinyHunters was also the cyber criminal in this case. The group claimed they have millions of documents, while Match called it a "security incident" that is still under investigation.
The family of Match dating apps finishes out the list of the major 2026 data breaches in January. ShinyHunters was also the cyber criminal in this case. The group claimed they have millions of documents, while Match called it a "security incident" that is still under investigation.
- Scale of breach: 10 million records
- Data exposed: User and corporate data
- Breach cause: According to ShinyHunters dark web leak site, it cited AppsFlyer as the entry point. AppsFlyer is a marketing analytics company for apps.
- Breach report: The Register published a review of the breach and exposures.
Key Lessons
It appears this is another third-party system failure. Data sharing for analytics is essential to any business but carries risk. Secure data exchange, internally or externally, with modern encryption allows for access while safeguarding data.