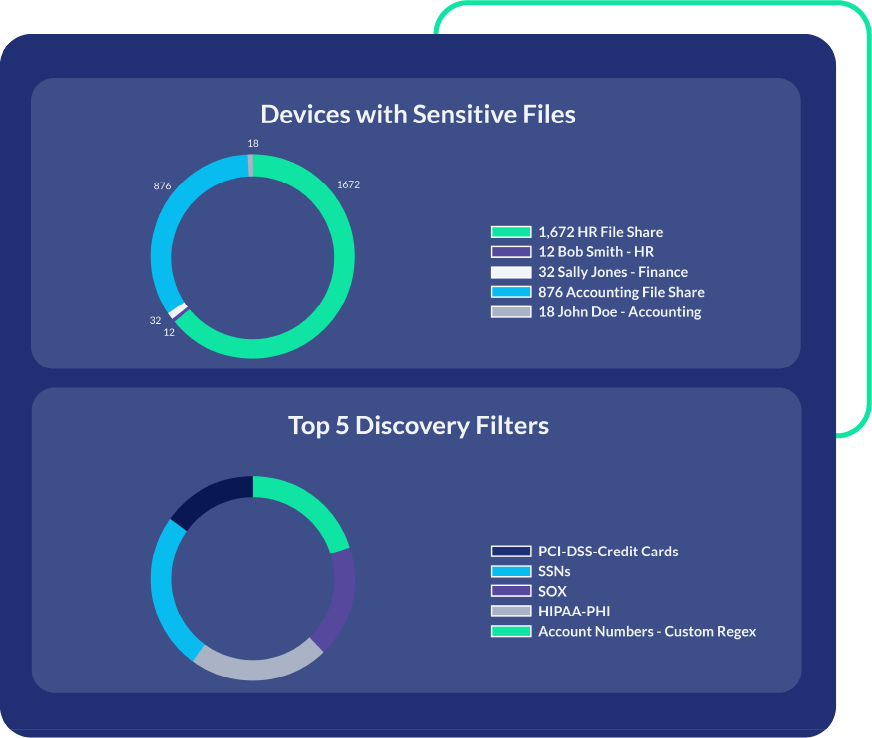
A Stronger Security Posture with Discovery You Can Trust
You can’t protect data that you don’t know exists. PK Protect automatically locates sensitive data across your organization. Accurate and comprehensive data discovery provides the visibility needed to take informed action.
Unmatched Coverage, Precision, and Performance
Complete Visibility to Enable Compliance and Reduce Risk

Centralized Policy-Driven Discovery
Use out-of-the-box sensitive elements to scan for PCI, HIPAA, GDPR, and most other compliance regulations. Build your own sensitive element definitions or tailor policies for specific requirements. Centrally defined policies allow consistent enforcement across all data environments from a single platform.
Discovery Without Moving or Copying Data
Discovery occurs entirely within the customer’s environment using an agent-based approach. There’s no need to move or duplicate data. Relocating or copying sensitive data increases the risk footprint and creates new vulnerabilities. By keeping data in place, PK Protect reduces these risks and delivers secure, in-place discovery.


Actionable Insights with Comprehensive Protection
After discovery, immediately remediate risk with a full spectrum of protection options. You can classify, encrypt, mask, redact, delete, or quarantine. Easily ensure compliance and safeguard data from a unified platform that automates data discovery and protection.